 Srnicek & Williams “Inventing the Future” made quite a stir when it was released, as did their Accelerationist manifesto. As usual, when I hear such excitement I am concerned, concerned that a lot of people are getting sidetracked by glamourous, new-sounding formulations, away from the very urgent work at hand, which is to understand, confront and usurp the material conditions for the reproduction of the present.
Srnicek & Williams “Inventing the Future” made quite a stir when it was released, as did their Accelerationist manifesto. As usual, when I hear such excitement I am concerned, concerned that a lot of people are getting sidetracked by glamourous, new-sounding formulations, away from the very urgent work at hand, which is to understand, confront and usurp the material conditions for the reproduction of the present.
Srnicek & Williams have done a great service. I strongly appreciate their call for a futuristic, left-promethean imagination, which attempts to promote a technologically advanced yet socially just civilization. However their notion of technology is too narrow. Granted, Veblenian leisure-class-envy will always be with us, and will provide endless fodder for the various real life soap operas which get our hearts pumping. However, in a (future, social) world where economic injustice is moderated by dutiful and earnest polity, unforseeable new forms of science and technology will become possible, which will engage us in socially culturally and materially productive activities we are incapable of envisioning today.
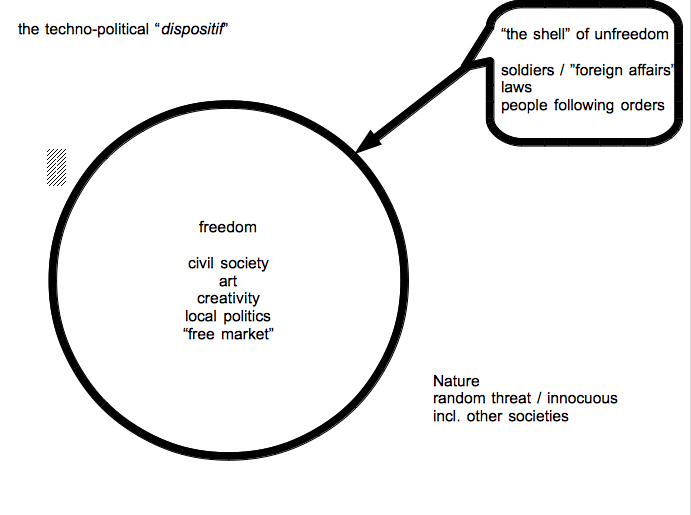
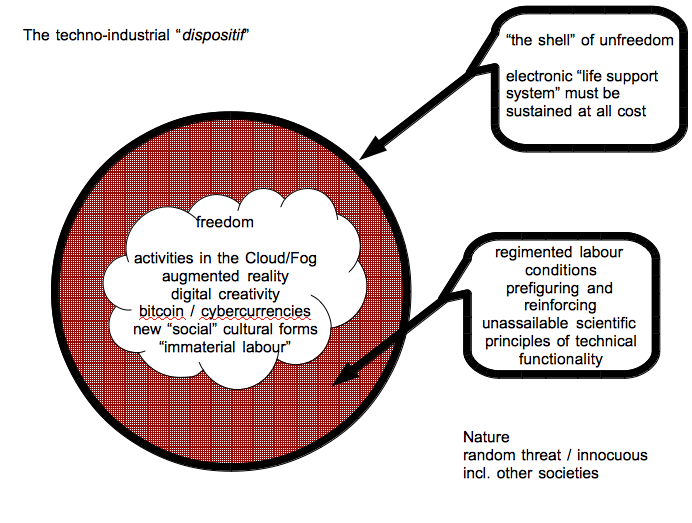
We do not need robotics, or “to do away with labour” for this to happen, we need to moderate economic injustice. However, under the prevailing conditions, where the vast majority of new technologies (the futuristic ones, at least) are always industrial and mechanical in nature, where the singular vector of “sensor everything”-and-AI-the-results-into-executable-drone-action prevails, where the notion of progress is overdetermined by regimens of security and defense, there only seems one way forward: new machines.
The problem with the vision of the abolition of labour by machines has been discussed as long as the vision has been projected. The robotics production chain today is still full of labouring human beings. Now, the conditions may not be so bad for those higher up in the production chain, but let us, as leftists, please not gloss over the persistent and, up until now intractable requirement for exploitation of the meanest forms of labour the earth has ever seen as we approach the bases of the production chains. The reasons that automated labour will not liberate us is because it is built with and thus perpetuates the conceptual world of extreme unfairness and despotism. A world predicated on slave/subservient labour will produce societies and cultures which justify this. The imagination of humanity emancipated from toil by slavemachines is a tyrannical one.
But left us grant that we need to be tyrannical to some extent since our enemy is to a large degree “Nature” whose unpredictability threatens to destroy us. How we prevail over the deleterious effects of nature was one of the original drives of science, and has generated so much of the essential knowledge providing some of us the leisure and opportunity we enjoy today. But there is a trade-off, one we are still ill-prepared to make.
We enslave nature, and thereby, “provisionally” we murmur, some segment of our own species (in principle equally invested with rights) . But we do not have the cultural technologies to understand the trade-off between enslavement and emancipation. In the coming era (probably brief) of a resurgence of left science as a backlash to neoliberalism, it is precisely such technologies we must cultivate.
Capitalism tightens the screws over and beyond the pain threshold, as it must. Once the economic pressure becomes unbearable, a left swing in politics inevitably ensues, as we are seeing now. This left swing must not be confused with a permanent revolution/evolution in human society/sociability. At best, the left palliative will be able to prevail for an election cycle or two, until, always under extreme duress from capitalist/plutocrat machinations it will cede the gains it had managed to produce (improved infrastructure, improved education, etc. ) again to re-neo-liberalised exploitation.
As we see today a new dawn of socialist consciousness across Europe and even in the USA, we need to prepare well to make sure some of the economic resources released for the social good actually are used not only for the high-ticket science that dazzles us, but on fostering and reproducing the earnest and studious science of engineering how socialism can be sustained (to thrive!) for longer than a couple of election cycles. We need to understand the contemporary and historic trade-off between capitalized labour and civic freedom, and we need to cultivate new technologies,, social and cultural practices which can help us sustain social and economic justice so that it prevails over and subsumes capitalist productivity.
Srnicek & Williams are impatient, this I understand. However, their appraisal of what they call “folk politics” is ungenerous. It is precisely that kind of folk politics which is powering Podemos and the Bernie Sanders campaign, which brought Syriza to power. Admittedly it is not enough and we need more than traditional street militancy to sustain socialist practices. However, visions or projects for teleportation, nano-surgery and socialist Mars colonies, are not going to convince capitalists to stop attacking socially produced value every way they can. We need more fundamental knowledge about how the present is reproduced in this first place, the legacy of colonialism, imperialism, patriarchy and slavery in the very devices we use to understand such things, and we need social and cultural technologies to integrate that consciousness into new behaviours, new sociabilities, new modes of exchange.
Their book has some good history in it. Even if your thesis fails, at least do some good history, then people will still read your book. But as far as the present goes, Srnicek & Williams. “demand” for Universal Basic Income is certainly inadequate. UBI is increasingly advocated by the Silicon Valley elite precisely because it enables more of the neoliberal withdrawal of state provisioning of social necessities. If you “choose” to spend your UBI on fast food and gambling and then end up unable to pay your rent, have a pension, have health care… its your problem, because there are no more social services to provide for you. UBI will have made it politically tenable to do away with them. A far stronger demand would be one for universal basic housing,universal basic education,universal basic health care etc.
There is no reason in an advanced economy why babies are born in debt for expenses they must incur only to live, and for which they must first prepare and then submit themselves to wage labour in order to “repay”. We already have the technologies which can allow us all to live on this earth at excellent standards, they are not evenly distributed, and even when they are, they are wastefully reproduced and employed.
If we are born with any legitimate debt, it is one we owe to the legacy of exploited labour, which, through centuries of colonialism, imperialism, patriarchy, and other oppression bequeathed us the brilliant affordances of today. Inventing the Future must happen in the present, it is the present which will afford us every future we can imagine. Therefore it is to the conditions of the present inhabitants of our planet we must attend, each and every one of them, with the same care and concern, and with all our intelligence and science, if we want to produce sustainable forms of emancipatory society under the contemporary conditions of extreme capitalist discipline.
—
If you would like to probe the intractable depths of these concerns, please consider my new book on ATROPOS PRESS “A Political Economy of the Smallest Things”